Nssm224 Privilege Escalation Updated -
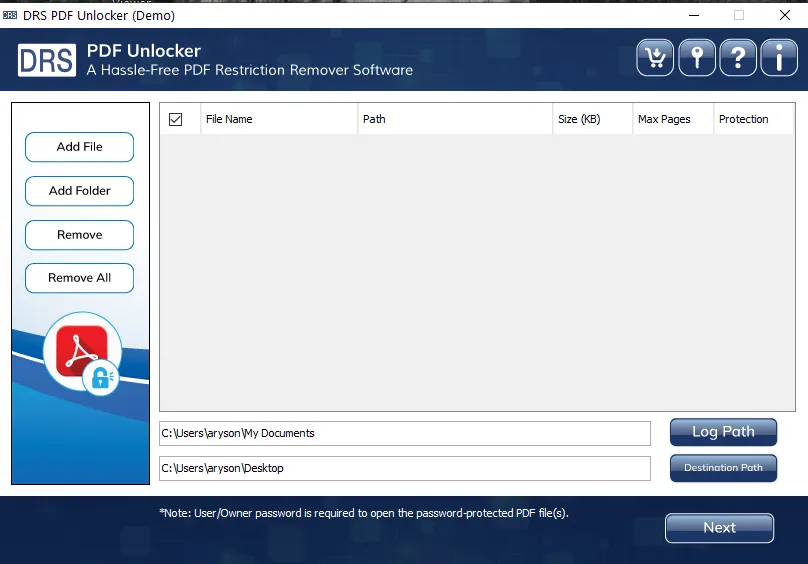
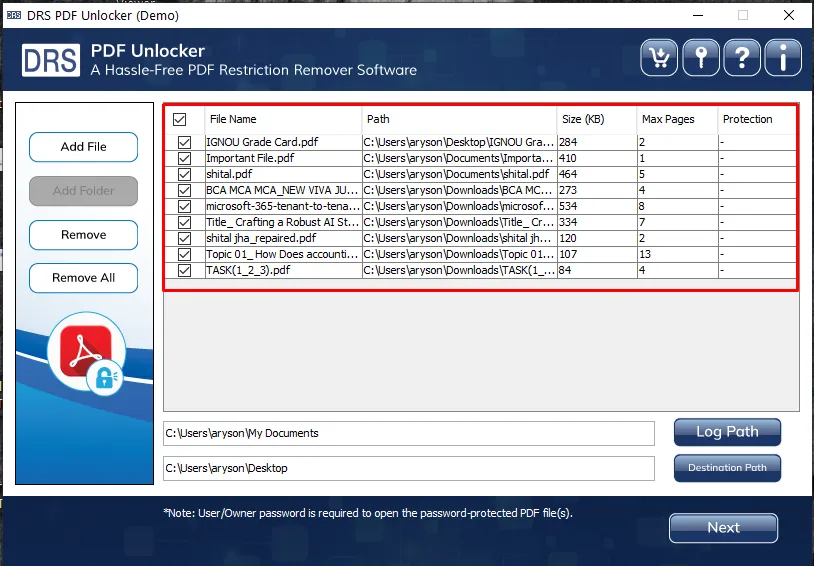
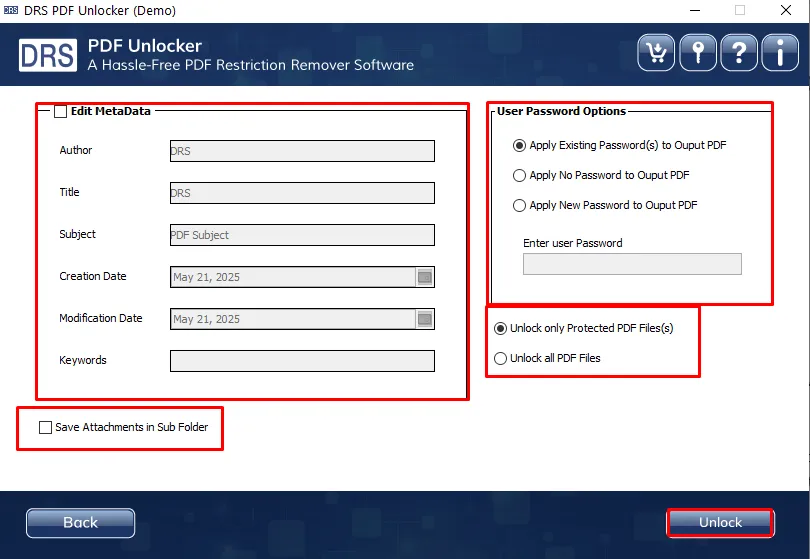
Effortlessly unlock secured PDF documents with the MigrateEmails PDF Restriction Remover Tool. This advanced solution removes both user-level and owner-level restrictions. That enables full access to editing, copying, printing, and content extraction while maintaining the original file structure. Designed to support batch processing, it allows files to be saved individually and offers options to retain or set new passwords. Fully compatible with all Adobe PDF versions and Windows operating systems.